Hands-on Hacking
-
I have gone through your CEH, only to find that its not so much practical driven, and even with this Hands on Hacking i find it difficult to follow as you hide basic details, eg what exactly is breach and how do i get it, is it an OS, because you didn't give a background, you just started working with it. I really need to get My hands on practical's, i tried following you on the wireless hacking but didn't understand your platform, even if it meant building my own lab
-
Greetings, @Joseph-Okwor
I'm so sorry to hear that there is any confusion as to the content of the CEH and/or Hands-On Hacking series. Hopefully I can clear that up for you.
Let's start with CEH.
This being a certification offered by EC-Council, it is EC-Council that creates the objectives for the certification. They also set level of mastery on each of those topics that is expected to be gained by the learner. I do my best to make sure that each of our episodes teaches to at least the minimum level of master expected for the learner to be successful on the CEH exam. That said, wherever it's feasible, I will make sure to demonstrate the objectives and explain the 'real-world' application of each. It just may be that the CEH isn't enough of a 'practically driven' course and your criticism would be better directed towards EC-Council. The objective of our CEH course is to prepare you for the CEH exam, and not necessarily to make you a 'practical' hacker. If I had all the time in the world, I would love to make the CEH course my magnum opus, but the amount of content that must be covered is just too massive in scope for that to be a reasonable task. (The official CEH courseware is like 5000 pages and doesn't go anywhere near the depths as I covered it).
Now to Hands-On Hacking.
This course is designed to work on building the learner's hacking methodology and application of skills that the learner already has, so there is an assumed level of knowledge for that course. This is talked about in the Overview video for that course. This is why I don't spend much time on details like whether or not something is an OS (with regards to Breach, I do mention at the beginning of the first episode that it is a vulnerable virtual machine that I downloaded from Vulnhub). Ironically, it's exactly the lack of details that makes the Hand's-On Hacking course valuable. I wanted to make a series that provided the learner a chance to test their hacking skills against an unknown environment. In the series we are learning about the target as we go in a true 'Black Box' test and using what we learn to take us to the next step, ultimately leading us to rooting the box. All that to say, Hand's-On Hacking isn't really for the uninitiated, but more for those looking to hone the hacking skills they already have.
Finally, Wireless.
Demonstrating wireless is a difficult task as there is no single platform that everybody uses. They're all different. This makes it impossible for me to 'show you' the exact thing you may be looking at. Because of this, I use the 'emulators' found a ui.linksys.com so that we can all be on the same sheet of music when discussing theory.
For demonstrations I need a live environment, so I'm forced to build a lab that you may not be able to recreate 1:1. All I can do is show you how it works in that environment and hope you're able to follow along and apply it to your lab. That said, if you have problems with getting your wireless lab working, feel free to reach out here and we will do our best to help you when/where we can!
I truly hope this helps you out and if you need clarifications please don't hesitate to ask your questions here.
Cheers,
Daniel -
Hello Daniel,
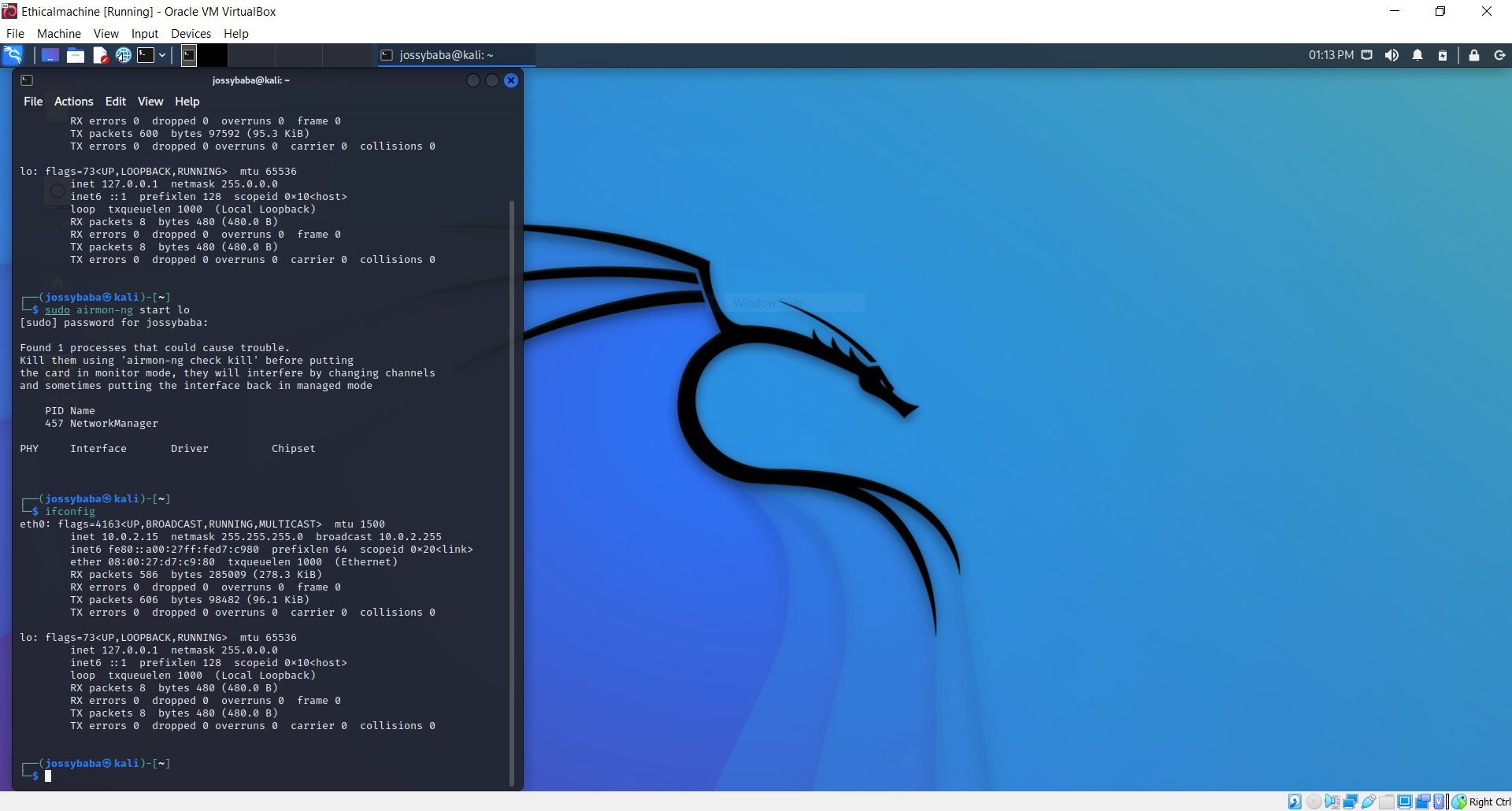
Thank you for your swift response, I must admit that i have enjoyed your show with Kitty, many regards to her, she is a great co-Host.On the Wireless Hacking in the CEH series, I will like to confirm that you were working from a kali machine, and when you did the MAC spoofing your wireless card name had a name you used, I remember you said most names will be wlan0, I had an issue because my VM gave me just lo and when I tried the steps you used I didn't get the same output. I couldn't enter the monitoring mode.
 I am using the virtual Box as my VM, does that have any meaning!
I am using the virtual Box as my VM, does that have any meaning!Please I will appreciate your help.
Joseph -
Hey @Joseph-Okwor
I'm so glad to hear you're enjoying the show and I will give Kathy your regards.
Now for your wireless issue. The problem you're having is most likely due to the fact that you're using a VM.
Virtualization platforms don't really virtualize wireless network adapters, they just create a virtual network adapter and connect to the host's wireless adapter using bridged, NAT, host-only, etc.
So when you do an ifconfig in your Kali VM, you're seeing the eth0 adapter which is that virtual network adapter and even though that may be connected to your host's wireless adapter, the Kali VM can't see it as such.
What you need is something like a USB wireless adapter. This will allow you to pass that connection to your VM and Kali will then be able to detect a USB connected wireless adapter, thus giving you wireless capabilities inside your VM. Alfa Networks is a great vendor that makes adapters that should work well for you.
I hope that helps get you going.
Cheers,
Daniel -
Hello Daniel,
Thanks for your response, I have gotten a wireless adapter, but I noticed that when my VM connects to the adapter, my laptop doesn't have connection, I will like to know if the adapter should have some special spec. or am I supposed to use this on a desktop that doesnt have a wireless card before. I am really feeling like partitioning my laptop right now.Joseph
-
Ahh, VirtualBox makes this kind of thing a bit more difficult than it needs to be.
Try following this guide to get you working.
I hope that works!
Daniel