CCNA ASA 5505 ping issue
-
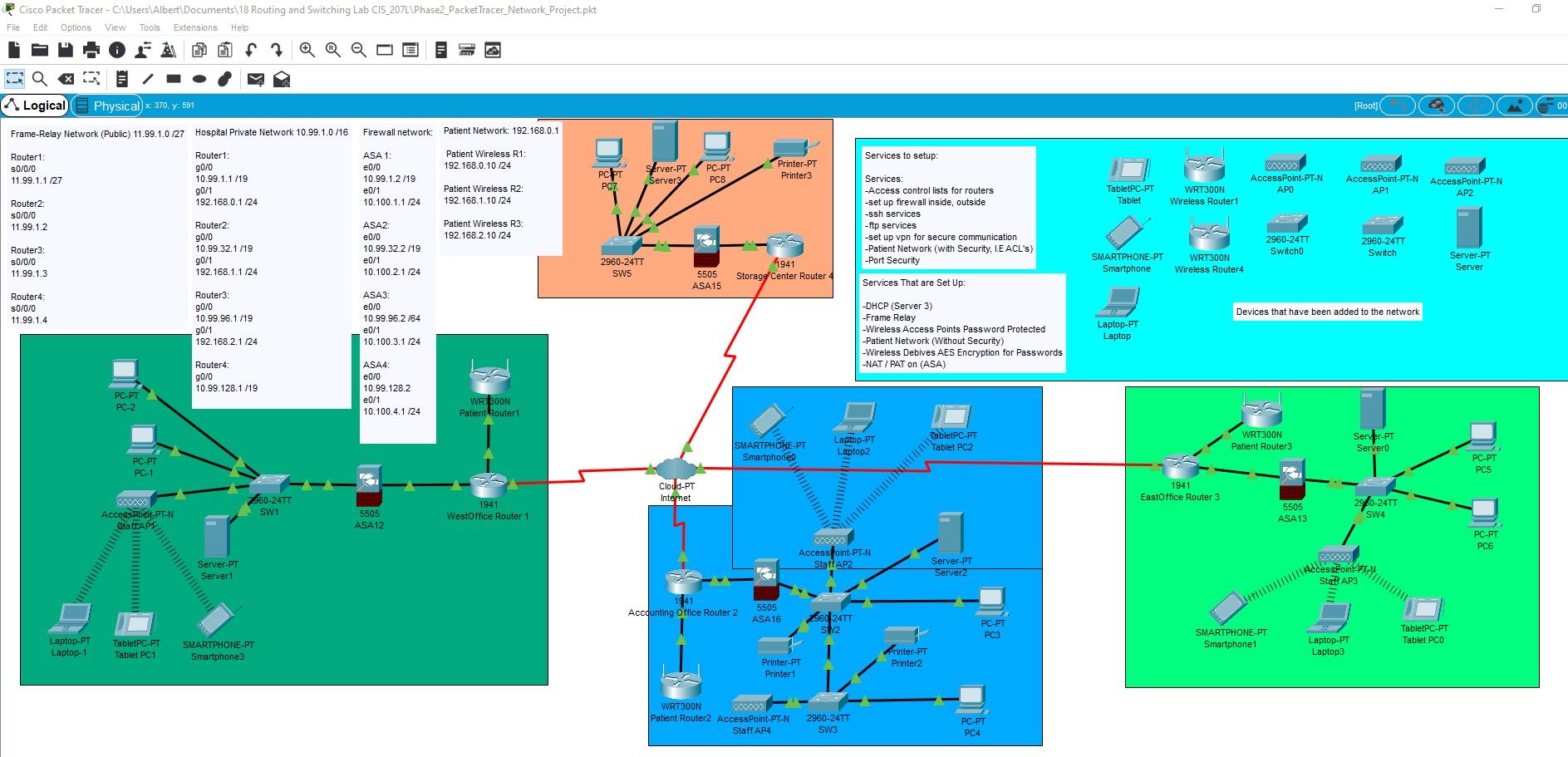
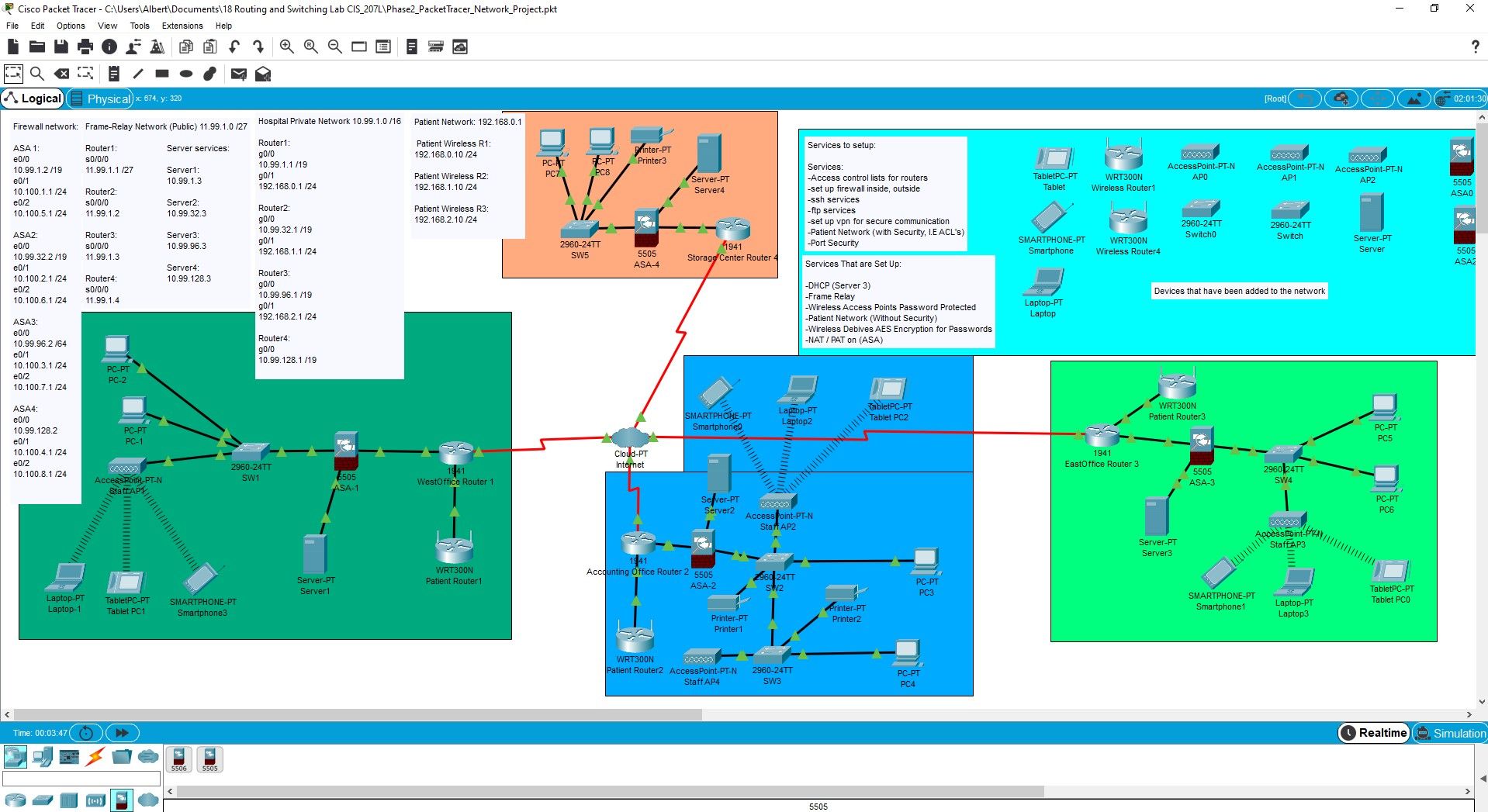
I have been working for hours trying to figure out how to configure my firewalls in packet tracer for the pretend hospital network I am building. The cloud pt (internet) is set up with frame relay going to router 1, 2, 3, and 4. from there you have the wireless router connected to the router directly for patient internet access. as you can see there is also a firewall connected which separates the private network of the hospital from the patient network. I am able to ping from any of the private pc's in the network to any other firewall, but unable to ping from private network to private network. Please help!!! There is a picture of the network along with the link to the actual packet tracer network to download, maybe help me troubleshoot the issue. Thank you in advance.
-
@Albert-LaScola said in CCNA ASA 5505 ping issue:
I am able to ping from any of the private pc's in the network to any other firewall, but unable to ping from private network to private network. Please help!!! There is a picture of the network along with the link to the actual packet tracer network to download, maybe help me troubleshoot the issue.
Ok... Apparently, the packet tracer file is not able to downloaded for viewing from outside of your sharepoint network. An error occurs. just a note.
So without the ability to try things. I believe that you what is happening here if the ASAs were just setup with the
outsideandinsideinterfaces configured, the default rule applies. That default rule is that all traffic originating from theoutsideheading to theinsideis going to be blocked.According to your diagram, I'm noticing that you've got your patient wireless routing on a different port that the port connecting to your ASAs...but your wireless clients are all connecting through your ASA....this unusual because it means that your APs and clients are on a different subnet than your wireless router...but that's another issue.
I would check your ASA rules and see if you allow traffic from the other networks to enter the
outsideof your ASAs. -
@Ronnie-Wong Thank you for your advice I will be checking the rules today and continue trouble shooting, I will also try to make the packet tracer file downloadable from the sharepoint.
I was trying to give the patients access to internet without having direct access to the actual hospital network, and the wireless access point on the other side is for doctors that need to connect via laptop or tablet to the private network to pull and update patient files. That was thought process I could not think of a better way to do it.
-
@Ronni-Wong New Packet Tracer Link
This should work fine now.
-
update I eventually got it to work. I created a DMZ and upgraded the 5505 license using this command:
"activation-key 0x1321CF73 0xFCB68F7E 0x801111DC 0xB554E4A4 0x0F3E008D"
I then created a static nat for dmz interface and then an access list with rules for icmp and http.
-
conf t
class-map inspection_default
match default-inspection-traffic
exit
policy-map global_policy
class inspectioin_default
inspect icmp
exit
service-policy global_policy global
int vlan 3
ip address 10.100.5.1 255.255.255.0
no forward interface vlan 1
nameif dmz
security-level 70
int E0/2
switchport access vlan 3
show int ip brief = ASA interfaces
show ip address = Layer 3 VLAN interfaces
show switch vlan = showing inside and outside VLANs, and the assigned ports
conf t
object network DMZ-Svr
host 10.100.5.2
nat (dmz,outside) static 10.99.1.3
exit
conf t
access-list OUTSIDE-DMZ permit icmp any host 10.100.5.2
access-list OUTSIDE-DMZ permit tcp any host 10.100.5.2 eq 80
access-group OUTSIDE-DMZ in interface outside
-
-
That's a good catch. NAT is usually a culprit when you cannot ping all the way across your internet connection to you the outside interfaces of another network but normally when you cannot reach past your default gateway. So this is a great catch.